When emulating macOS on Proxmox, it seems that we are forced to set the guest’s CPU type to “Penryn”. This is a very old architecture, and is missing some features that could unlock higher CPU performance. In particular, I wanted to use AVX (for accelerated stream processing) and AES-NI (for encryption), but macOS panics on boot if I set the CPU to Sandy Bridge, which would match my CPU which includes those features.
Luckily, kholia over at the OSX-KVM project has discovered that we can keep using Penryn, but enable the passthrough of individual advanced CPU features and have Sierra use them, even though Penryn never supported these features.
See his guide here:
https://github.com/kholia/OSX-KVM/blob/master/notes.md
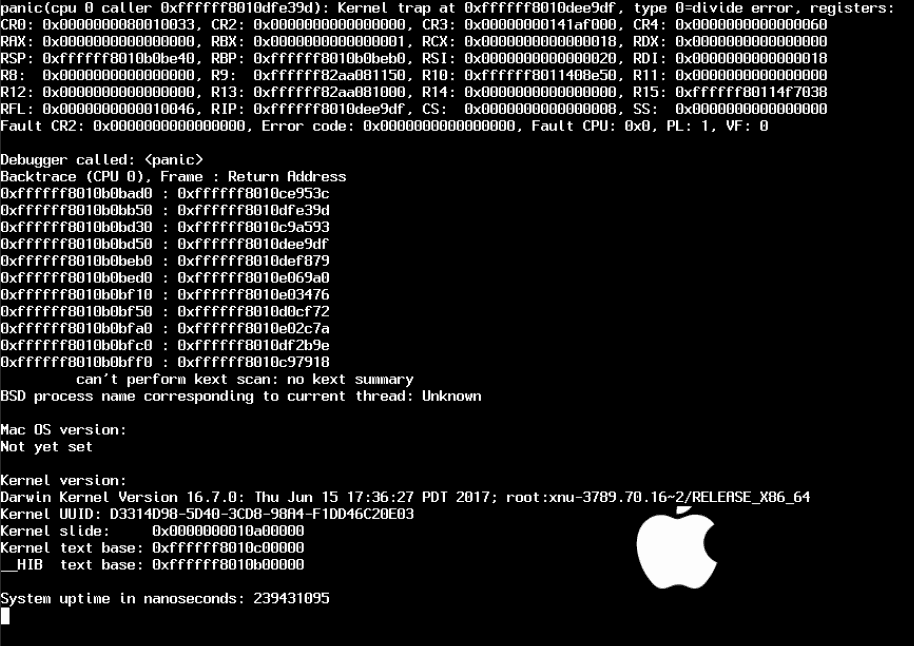
One stumbling block for me was that my VM only seemed to boot correctly if the “machine” type was set to “pc-q35-2.5”. Using any newer version caused a division by zero error during early boot:
pc-q35-2.8 or newer is required to pass through AVX and AES-NI, so I was stuck. However I finally realised that my VM would boot correctly using the newest pc-q35-2.9 version if I set the “core” count to 16 or fewer.
I have two CPUs, both with 8 cores and 2 threads per core, and I was trying to pass through 32 threads in total. Since Proxmox doesn’t support setting the number of threads, I was doing this by passing through 32 “cores” on one emulated socket, which worked fine on pc-q35-2.5, but failed on any newer version.
To solve this, I set sockets to 1 and cores to 32 in Proxmox’s VM settings, but then added my own “-smp” option to the custom “args” in order to override the CPU layout and set the number of threads per core correctly. Here’s my completed args for the passthrough of AVX and AES-NI with 32 threads:
args: ... -cpu Penryn,kvm=on,vendor=GenuineIntel,+invtsc,vmware-cpuid-freq=on,+avx,+aes,+xsave,+xsaveopt,enforce -smp 32,sockets=1,cores=16,threads=2 sockets: 1 cores: 32
There are more options that can be passed through on newer CPUs, including AVX2 (see kholia’s guide for details), but these are the options that work for my Sandy Bridge-EP system.
Note that the kernel mitigation for the 2018 Intel CPU vulnerabilities Spectre and Meltdown is said to use the “pcid” CPU feature to reduce the overhead of working around the vulnerability, so pass that one through too!
Note: I also had trouble passing through strange numbers of cores to macOS, like 14, I’m not sure what’s going on there. Maybe it’s checking against a list of supported CPU topologies?

Is there an explanation for why using any other CPU besides Penryn causes MacOS to crash? I find it odd that using Sandy Bridge causes your Mac install to crash since MacOS officially supports Sandy Bridge.
I haven’t seen one, no. The last time I looked at the Clover source, I think I remember seeing some code which handled Penryn combined with QEMU detection as a special case, so that might be the only CPU they fix up for macOS to consume.
My setup with cpu: host “works” with the latest Clover. My host CPU is a Xeon L5640, Westmere-EP. However, CPU usage is very high (running at a constant 80 to 100%) . But, this may suggest progress is being made in Clover. Much has improved since even very recent Clover revisions with QEMU.
I can also get it working when using the host identifier as CPU with my i5 8600K however it seems to not perform as well as Penryn as I get random lags in the host (despite benchmarks and such showing higher numbers).
I think this is is because the CPU topology is not correctly sent to the guest. When using host, I’m seeing 6 sockets and 6 cores show up in System Information. So macOS thinks I have 36 cores across 6 sockets. Unfortunately, setting the proper topology in my case seems to result in a kernel panic. I can only set the topology when CPU type is set to Penryn.
The only reason I was messing around with this, is because I can’t seem to pass through all 6 cores on my CPU with Penryn. 4 works fine.
Could you do a more in depth ‘howto’ on this? i am not a mac user and his ‘guide’ is clear as dirt.
If you’re not a Mac+Proxmox user then this guide doesn’t apply to you.
i am very much a proxmox user, and i am TRYING to be a MAC user but i have very litle MAC experience. i would like to speed up my VM as it does not seem supper responsive.
for those who were confused by this page, just adding the lines to your ###.conf file in proxmox is all that is needed. no changes inside the OS. then you can check that it worked by running the command “sysctl -a | grep machdep.cpu.features” inside the osx vm. you should get a list that includes things like SSE3, MMX, and the new things you passed through like AES and AVX1.0.
What about VMX and nested virtualization?
As the configuration posted, Docker (That requires vmx to run) can’t be used.
Would be nice to have in a mac vm in order to use it for development.